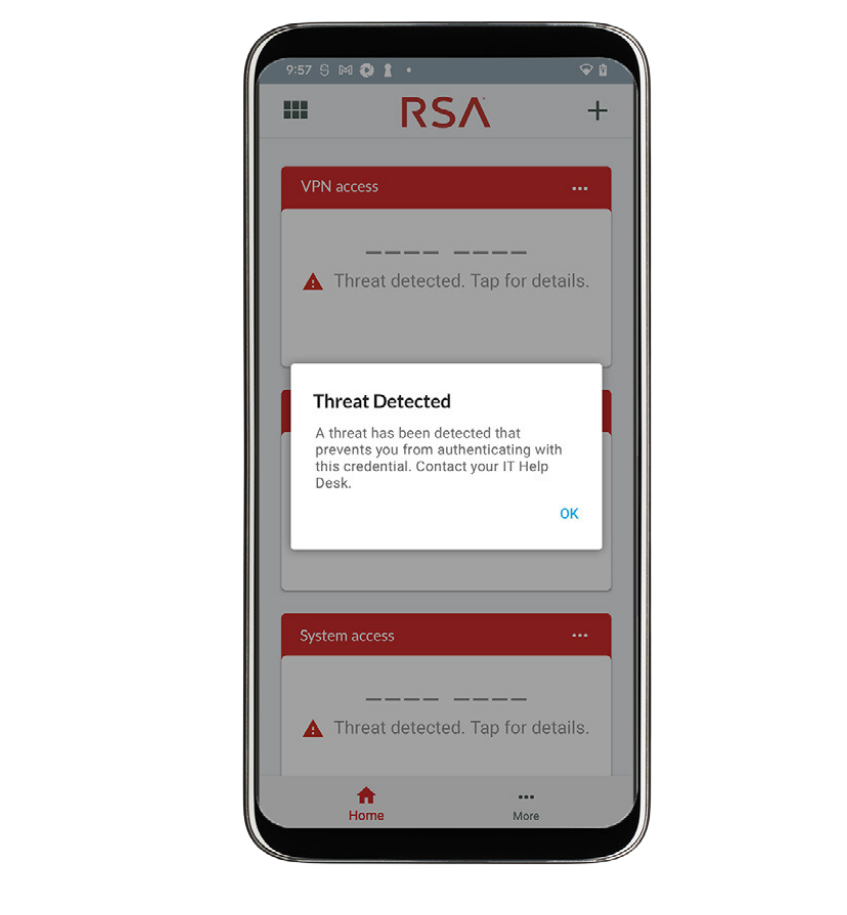
RSA Mobile Lock
RSA Mobile Lock detects critical threats to a mobile device and restricts the user’s ability to authenticate until the threat issue is resolved, allowing IT to establish trust by verifying mobile devices across the attack surface, systematically protecting against threats, and securing any device to mitigate those threats.